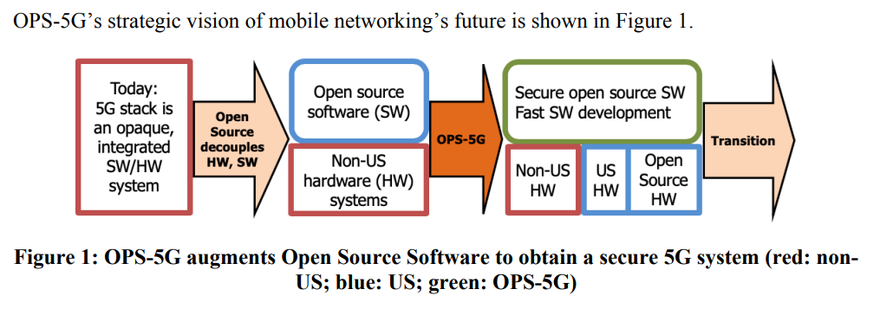
US military research agency DARPA plans to launch an open source initiative to help secure upcoming 5G networks.
OPS-5G aims to lead to the development of a portable standards-compliant network stack for 5G mobile that is open source and secure by design. The "long-term objective is a US-friendly ecosystem" featuring a trillion networked devices, a broad agency announcement for the four-year project states.
Securing 5G
The Defense Advanced Research Projects Agency is looking for research partners for the Open Programmable Secure 5G program, which is expected to begin in October 2020 and span three phases - two 18 month stretches, followed by a 12 month final phase.
"Standards processes are used to maintain interoperability required for a public network, and while many of the components and component behaviors of 5G have changed little from predecessors such as 4G and LTE, the standards for the most futuristic 5G features are those most in flux," a document detailing the project notes.
"These futuristic features also present the greatest risk to US national security, as networks are simultaneously critical infrastructure and the means used for cyberespionage and cyberwarfare."
To combat this risk, "OPS-5G changes are focused on increasing trust at a set of soft points that include unmanaged, unattended, long-lived, and possibly long-forgotten IoT devices. Additionally, OPS-5G addresses unintended and unwanted interactions between network slices and threats from the vast increases in network scale."
The program is split into four technical areas (TAs):
- TA1 aims to reduce the time open source updates can take to hit the market;
- TA2 looks to create a zero-trust security architecture for devices from IoT sensors to servers;
- TA3 hopes to mitigate against new attack surfaces (such as side-channels) introduced by virtualization and slicing;
- TA4 seeks to change programmability from being a threat vector to instead being "an enabler of security at scale."
Potential DARPA partners have to send in proposals for the technical areas separately - and can aim to work on just one TA, or a combination.
TA1 performers will be examined by the Independent Test and Evaluation team. "OPS-5G TA1 will focus on accelerating open source software development with machine translation of 5G standards documents. 5G standards are maintained online as a set of electronic documents and updated as needed. As operational 5G software must be standards compliant, updates in standards spur new software development."
TA2 applicants are expected to "describe and justify security architectures that operate across all scales of nodes and networks, minimizing use of 5G core network services, and maximizing use of mobile edge computing (MEC) to avoid performance bottlenecks from shared central services."
The proposed "architectures should support low-cost, unattended, long-lived, battery-powered sensors, which will be the smallest, cheapest, and most numerous devices in the 5G ecosystem."
For TA3, DARPA notes that performance requirements of mobile networks can vary wildly - for example, with video streaming the user's device can store some of the video as a buffer, allowing for some bandwidth issues. A tele-robotic surgery, meanwhile, cannot suffer any such difficulties. TA3 proposals should take this into account, as well as the fact that "an imaginative adversary might use novel or unknown methods for extracting information."
TA4 hopes to address the reality that OPS-5G aims to use of network functions virtualization (NFV) and software-defined networking (SDN) technologies, something that should accelerate its network evolution, but could also open it up to attack.
"The consequences of introducing programmability with insufficient attention to malicious actors and their capabilities is illustrated by the addition of scripting languages to web browsers," DARPA's document cautions. "Initially intended to customize local behavior of downloaded Web content for presentation by a web browser, the execution of programs of unknown provenance has opened hosts to a multiplicity of security threats."
In particular, TA4 proposers should plan to design and prototype a scalable Distributed Denial of Service (DDoS) defense for 5G networks. DARPA cites the damage caused by the Mirai botnet, which used 600,000 IoT nodes to deliver 623Gbps of packet traffic against a target server (taking out a host of websites). "In light of this, the vast increase in IoT devices connected via 5G represents a significant threat."
Slides from an OPS-5G proposers day warn: "5G will have 60-600 billion (!) nodes by 2023!!"
While TA2 should theoretically stop OPS-5G devices from being recruited into botnets, TA4 should also seek to counteract any botnets formed by non-OPS-5G devices. "TA4 technologies will enable scalable resilience by detecting the onset of DDoS attacks with in-network sensors and deploying active in-network defenses in response."
TA4 will be evaluated using 5G testbeds at US government facilities. One such site, mentioned elsewhere in the document, is a 5G test program at the Naval Information Warfare Center Pacific. Separately, the Department of Defense in October said that it will begin a “large-scale” effort to explore various applications of 5G technology, trialing equipment at four undisclosed domestic military bases.
By October 2024, OPS-5G is expected to be complete, with all work products and deliverables produced by the program, such as software, documentation and generated technical data, to "be provided with a license and rights acceptable to an open source consortium."
The final milestone is the "commercial availability of the OPS-5G stack in at least one mobile network operator and in user equipment as appropriate."
Funding for the project has not been determined, with applicants expected to provide their own cost predictions for their work. Multiple awards are anticipated for each of TA1, 2, 3 and 4.
The program is currently being managed by Dr. Jonathan M. Smith, who was previously involved with the DARPA projects Situation Aware Protocols In Edge Network Technologies (SAPIENT), Adaptive Cognition Enhanced Radio Teams (ACERT), and Brood of Spectrum Supremacy (BOSS).
The dragon in the room
Unmentioned in the broad agency announcement is the fact that the whole program is essentially a response to a certain rival superpower's success in 5G technology.
China has pumped billions into 5G infrastructure, outspending the US by roughly $24bn according to Deloitte. Its potential dominance over the future of connectivity has ignited fears throughout the US security community.
Huawei, in particular, has spooked US spooks. Government officials have long claimed that Huawei acts as an arm of the Chinese state, an allegation it vehemently denies.
The US, which put Huawei on its Entity List (nominally due to allegedly evading sanctions with Iran) last year, has launched a concerted campaign to convince its allies not to use the company's equipment, and threatened to withhold intelligence data from countries that embrace Huawei.
The efforts have led to some total or partial bans, including in Australia, Canada, and Japan - as well as the United States itself. Citing national security, the country has never provided proof for its allegations, which date back a decade.
But - with Huawei equipment much cheaper than rivals, and arguably sometimes better - the allure of Huawei's tech has proved too enticing for even the US's closest allies. In January, the UK said that it would allow the Chinese telecommunications firm to build out 35 percent of its "non-core" 5G network, despite intense US lobbying.
In a congressional hearing last week titled 'Losing Ground: US Competitiveness in Critical Technologies,' former Google CEO and current chair of the National Security Commission on AI and the Defense Innovation Board, Eric Schmidt, said: "In infrastructure, I'll just be blunt: We need an alternative to Huawei; we need a US alternative that we're proud of."
He said: "I simply want America to win. What is it going to take?"