The Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency has big plans.
In an extensive briefing to vendors, attended by DCD, the US government’s cybersecurity division outlined its roadmap for the next five years, with the division expecting to increase in size, budget, and shift to the cloud.
All in on cloud
The talk, held over Adobe Connect last week, was led by Bryan Ware, CISA’s new assistant director for cybersecurity.
Ware previously worked with defense contractors on projects like the Star Wars program, early drone payloads, and counterterrorism technologies. In 1998, he founded an AI startup that which was acquired by Haystax in 2013.
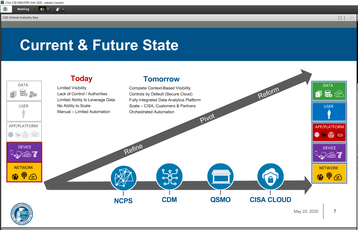
In Ware’s telling, CISA is stuck in the past. Many of its protocols and tools were set up five or six years ago, before government’s big push for cloud computing. “From that environment, we created these programs to address the threats and the risks that we saw,” Ware said.
“And over the last five or six years there has been this acceleration of encrypted traffic, this acceleration of moving to the cloud,” he said. “We've seen adversary shift their tactics and strategies. And so that picture that we're seeing is really helping us to refine the strategy that we want to execute on, the strategy that we believe is going to put us in the position to secure not only today, defend not only today but also to get into that posture to secure tomorrow.”
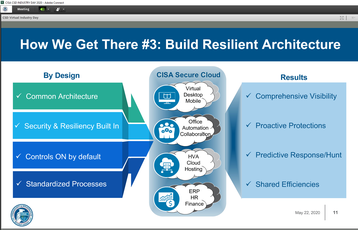
That will require CISA itself shifting as much as possible to the cloud, Ware said. “Having worked in other parts of the US government and commercial industry before coming to CISA, we're a bit of a slow or a late adopter of cloud,” he said. “And so we are very aggressively now working to significantly expand our cloud capabilities.
“That is everything from using the cloud ourselves to working with all of the vendors to understand how to best secure the cloud so that the way that we use the cloud is not only about efficiency, but that we're gaining security benefit.”
Martin Gross, associate director of capability delivery, explained that the agency’s cloud approach will be hybrid. "And when when I say hybrid, I mean that it's going to be virtualized on site, using multiple vendors, off-site, commercial government, and then also hybrid from the perspective it's going to be Infrastructure-as-a-Service, Software-as-a-Service and Platform-as-a-Service.”
He added: “It's going to be the full range of cloud offerings depending on what we have to do, how sensitive data is and where it needs to be and what customers we're servicing with our capabilities.”
It’s in that last point that CISA hopes to have the biggest impact - not just in upgrading its cloud capabilities, but those of all the departments and agencies across the sprawling US bureaucracy.
A matter of QSMO
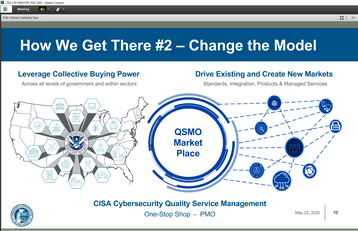
Earlier this month, the Office of Management and Budget designated CISA as the Quality Service Management Office for Cybersecurity Services, specifically Security Operations Center standardization, Vulnerability Management standardization, and DNS Resolver service.
In essence, this QSMO aims to serve as a storefront for all agencies looking to acquire commercial and non-commercial cloud and cybersecurity services. “So that we can provide that whole stack all of the products and services that you as an department or agency would need to know that you are operating securely and operating in a resilient way,” Ware explained.
“And so to build a QSMO, we have to build new business models, we have to build flexible ways to procure and to deliver those products and services. That's kind of the front of the store. But just as important - and maybe more important - is the back of the store,” he continued.
“We have to change the way that we find those products, the way that we scan for technologies and emerging technologies, the kinds of vendors that we're working with,” he said. “We have to find the ways to pull old products that are no longer meeting modern threats and risks or meeting our performance guidelines.”
Ultimately, CISA wants to “get to the place where we're buying on behalf of the entire US government,” Ware said. “And with that buying power should come the ability to drive efficiencies and to drive standardization.”
Ware warned that it was early days, and much was still up in the air. But, he told Industry Day attendees that included Raytheon, Northrop Grumman, and Juniper Networks, "I really feel like we're at an inflection point right now. We're at the ground floor, we're looking for you to partner with us in this really key moment."
Expanding power
Another roadblock to success is that most of what CISA does is voluntary - both for other agencies, and for the companies it tries to police. “When we're delivering services and capabilities to industry, we're not compelling them as their regulator,” Ware said. “We're not compelling them as a law enforcement agency, we are really designed to be and strive to be their cybersecurity partners - and so the same is true with the departments and agencies.”
That said, however, Ware does expect the agency to see an increase in power. “In some cases, CISA - and really the rest of the US government - just don't have the authorities that we need, in ways that are sometimes unexpected, to be able to provide the kind of cybersecurity to the nation that we’re expected to.
“Now, I would say that those authorities are growing and expanding constantly, and there are authorities that we have that we haven't taken full advantage of.”
With its shift to the cloud, the agency hopes to have far greater visibility across the government's various networks. "We need to see where the attackers are, we need to see where the unpatched vulnerabilities are. And again, we have a tremendous amount of coverage, but we just don't have it as completely as we'd like to have."
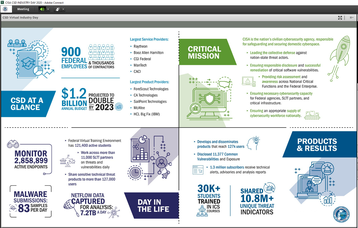
Another increase in power will come in the form of an increase in staff numbers - “we are one of the fastest growing parts of the US government right now, and I expect we will be double this size in just a few more years” - and a large jump in funding. CISA's Cybersecurity Division currently has roughly a billion dollars a year. "We expect that to double by 2023," Ware said. "But we also have $100 million R&D program with [DHS Science and Technology] in addition to that, [a lot of which is] in the area of cloud analytics.”
In the short term, CISA is also looking to obtain additional funding to fight Covid-19-related cyber attacks, Matt Kelley, associate director of cyber strategy, said. “Covid will increase our budget. You guys have seen some of the alerts that we've pushed out, and some of the analysis that we've done - there is an increased level of adversary activity against specific critical infrastructure.”
As the briefing drew to a close, Ware gave one more impassioned plea for more corporate collaboration with the public body. “I believe the most exciting days and most compelling work are ahead of us, and we want to be your best customer. We want to be the agency that everybody wants to work with.”