We all want choices—at work and in our personal lives. But psychologists have shown that having to choose from among too many options doesn’t necessarily make people happier or even result in better decisions. Psychologist Barry Schwartz calls it “the paradox of choice.” Cloud computing is bringing new options to enterprise IT organizations, but along with them it’s bringing the paradox of choice.
For most, “the cloud” means public cloud services. But Gartner predicts that by 2020, 90 percent of organizations will adopt hybrid infrastructure management capabilities. For Intel—and for most enterprises—that increasingly means a hybrid computing environment where public cloud services link to and share data and applications with private, on-premises clouds.
As we move toward hybrid environments, IT must have a rational methodology for evaluating an application and selecting the best deployment location. In more than 125 focus groups comprising Intel customers and system integrators, we worked to uncover the criteria organizations must consider when making workload placement decisions and to create a model we can apply to identify a starting point for workload placement. I say a starting point and not a formula, because every organization is unique, and your ultimate decision must consider factors unique to your organization.
The cloud cornucopia
First let’s look closer at the choices IT organizations face.
Public clouds provide infrastructure-as-a service (IaaS) offerings that let you spin up virtual servers and storage on demand and pay only for what you use. Providers now bundle databases and other middleware to create platform-as-a-service (PaaS) options that ease deployment by providing much of what’s needed to create functional applications.
Software-as-a-service (SaaS) solutions provide the entire application. Users just have to log in and use it, although integration with enterprise systems like security and identity management may still be required. Finally, on-premises private clouds use cloud technology and automation to deploy and manage applications to achieve resiliency and agility. But since it’s all in your data centers, you retain control.
Several commercially available hybrid cloud solutions can make public clouds a transparent extension of your on-premises private cloud. Common development tools, middleware layers, and deployment processes span the entire environment and insulate application teams from having to provide for or even be aware of an application’s eventual deployment location. You can choose a deployment location based on business needs and value, and you can change it if needs and economics change. But in making that choice, you must evaluate both business and technical considerations.
Business considerations
As technologists, IT professionals are quick to focus on the technology. But the objective is to place a workload where it produces the most business value, so it’s important to first identify the business factors that bear on the decision. Business considerations vary by industry and from company to company, but here are some things our study participants said were important to them.
First consider ability and suitability. When evaluating a SaaS solution, for example, do offered solutions meet the business’s needs and requirements? Do they reduce costs or otherwise represent a good investment for the corporation by freeing up resources for other business initiatives? You must realistically assess whether the organization possesses the expertise to achieve the workload placement goal and whether that expertise is available to the project.
Consider the size and maturity of your organization along with your financial strategy. Are you due for a technology refresh or major IT modernization? Are capital funds available, or is the CFO trying to direct capital spending to other initiatives? Would more on-premises hardware require data center expansion or construction? Are there legal requirements unique to your industry or your business that you must consider? How tolerant are the users of potential availability and performance issues? Could they work around short periods of unavailability, or does everything come to a halt if an application is down? And how risk adverse is the organization? Would an outage result in reduced revenue? Would a security breach damage your reputation or brand?
Business considerations like these provide a backdrop on which technical factors can be identified and evaluated.
Technical considerations
Technical considerations may be easier for most IT organizations to assess. They include:
Performance Public clouds are based on shared facilities, so performance can be less predictable and harder to assure. The response time experienced by users is the most visible measure of performance and can vary depending on where users are located. Public clouds can offer higher levels of performance, but it usually comes at higher costs. Applications that have the potential to bottleneck on CPU or memory may require dedicated hosts and be more suited to private cloud deployment where you can tune latency and performance to match the application’s needs.
One of the most appealing aspects of public clouds is their elasticity—the ability to acquire resources and grow utilization when needed and release them when no longer needed. So workloads that experience seasonal, temporary, or unpredictable demand should be identified and may be more suited for public cloud deployment. However, you should monitor service utilization, since it’s estimated that 30 percent to 45 percent of public cloud costs are attributed to wasted or unused cloud services.
Public cloud service providers recognize security as a primary concern of their customers, so most have built extensive security and security monitoring features into their service. Hundreds of engineers per cloud service are constantly working to build better security solutions and services for end users. But still, running workloads on public clouds represents an expansion of the attack surface that offers attackers more opportunity to find a way in.
With on-premises private clouds, the security protections you provide may or may not be better, but they’re under your control. You know where the data is and can assure and demonstrate compliance with regulations, data sovereignty dictates, and corporate governance requirements. And you can perform audits to assure promised controls are in place and being enforced. You must understand and provide for the special security needs of individual workloads. For example, if the data used by the application includes intellectual property, personally identifiable information, or personal health information, it may be subject to special requirements imposed by your organization or by government or industry regulations.
Many applications share or exchange data with other enterprise applications or are tightly integrated into internal workflows. Shifting them to a public cloud or acquiring a SaaS solution may necessitate a development project to integrate them with other apps or into existing directory, identity, and single sign-on systems. You’ll have to determine if APIs exist that can be exploited to achieve integration or if an enterprise integration framework can be used.
How much data is currently being stored and moved, and how much do you expect the data volume to grow? Positioning data close to where it’s going to be used improves accessibility, reduces latency, and holds down costs.
To better understand and categorize data, many companies are now employing a chief data officer. This corporate officer is responsible for enterprise-wide governance and utilization of information as an asset via data processing, analysis, data mining, information trading, and other means.
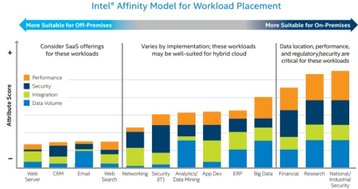
The workload placement affinity model
Applying the technical considerations to many common types of applications, we developed an affinity model that suggests the kinds of apps more suitable for public cloud deployment, those that should probably remain on premises, and a middle ground where applications might go either way in a hybrid cloud environment.
For each application type, the significance of each of the four technical considerations is reflected by the height of its component in the stacked bar. (For example, email apps are characterized by a large data volume but less critical performance, security, and integration needs.)
The affinity model explains why applications like Web hosting, CRM, and email are commonly acquired as SaaS applications, whereas big data analytics and financial applications tend to fall at the other end of the spectrum.